Struggling to keep your sensitive information secure in your Kubernetes cluster? Look no further than Kubernetes External Secrets. This handy tool makes it a breeze to store and retrieve secrets outside of your cluster, giving you added security and flexibility.
In this article, we’ll dive into the advantages, best practices, and limitations of using Kubernetes External Secrets.
Get ready to elevate your Kubernetes secret management!
What are Kubernetes External Secrets
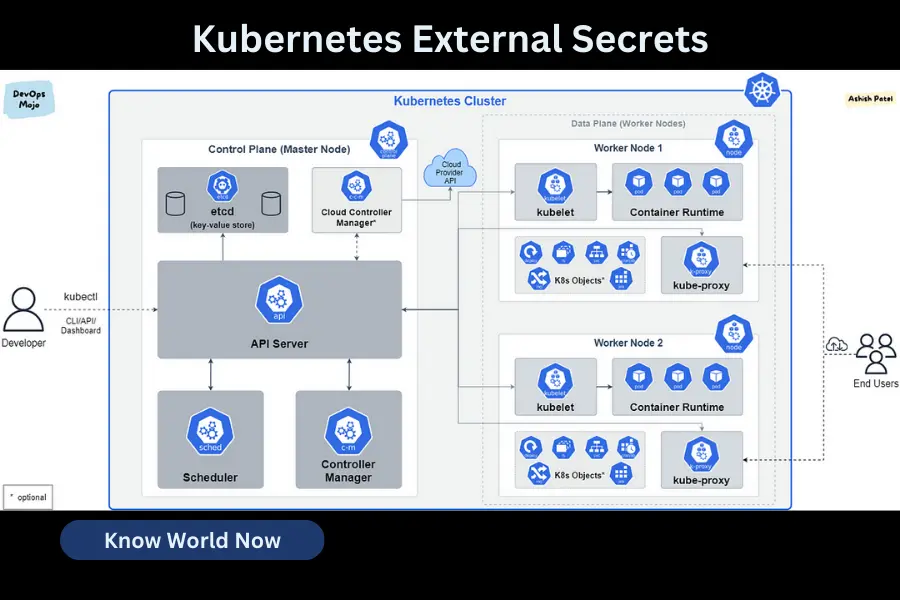
Kubernetes External Secrets is a feature that allows you to store sensitive information outside of your cluster. This helps you manage secrets in a secure and scalable way by integrating with cloud providers. It ensures that sensitive data, such as API keys or database credentials, are encrypted and protected from unauthorized access.
Kubernetes or K8s is an open-source, production-ready platform that helps automate the deployment of containerized applications and harness the many cloud computing benefits.
Storing secrets externally reduces the risk of exposing them within your cluster. This feature is particularly useful in scenarios where multiple clusters need access to the same secrets or when secrets need to be managed separately.
Some real-world examples of using Kubernetes External Secrets include securely storing database credentials, integrating with cloud provider secret managers, or managing API keys for external services.
Benefits of Kubernetes External Secrets
Developed by Google, the Kubernetes platform has been around and used by the tech giant for over 15 years. It is currently under Cloud Native Computing Foundation and combines the experiences and best practices of the vibrant K8 community. Kubernetes is continuously growing and is fast becoming the standard in containerized technology. Developers of enterprise Kubernetes platform Kubersphere stressed that.
Using external secrets in a Kubernetes environment has several benefits.
1. Improved security: Kubernetes External Secrets allow sensitive data to be managed by external services outside the Kubernetes cluster, reducing the risk of unauthorized access.
2. Easier management of secrets: Kubernetes External Secrets simplify the management of secrets by allowing them to be stored in external systems and synchronized with Kubernetes.
3. Decoupling secrets from application code: Kubernetes External Secrets help decouple secrets from application code and reuse them within the cluster when needed.
4. Centralized, robust mechanism for managing secrets: Third-party secrets-management systems are a better option to have a centralized, robust mechanism for managing secrets.
5. Supports multiple external secret management systems: Kubernetes External Secrets support external secret management systems like AWS Secrets Manager or HashiCorp Vault.
6. Provides Prometheus metrics for monitoring: Kubernetes External Secrets provide Prometheus metrics for monitoring.
By leveraging Kubernetes External Secrets, organizations can improve the security and management of sensitive data in Kubernetes clusters.
How to Manage Kubernetes External
Here are the steps to manage Kubernetes External Secrets:
Step 1: Configure an external secrets backend
To use Kubernetes External Secrets, you must configure an external secrets backend, such as AWS Secrets Manager or HashiCorp Vault. Access to the secret backend can be granted in various ways, such as granting your nodes explicit access to your secrets using the node instance role or directly providing AWS access credentials to the kubernetes-external-secrets pod by environmental variables.
Step 2: Create a Kubernetes Secret object
Create a Kubernetes Secret object that points to the external backend. Kubernetes External Secrets fetch and synchronize secrets from external systems, making them available as native Kubernetes Secrets.
Step 3: Install Kubernetes External Secrets
Install kubernetes-external-secrets to be able to retrieve your secrets. Once you have kubernetes-external-secrets installed, you can create an ExternalSecret object that specifies the name and location of the external secret.
Step 4: Use best practices
Avoid hardcoding secrets and use a tool like the Kubernetes External Secrets operator to manage secrets.
By following these steps, you can securely manage sensitive data in a Kubernetes cluster using Kubernetes External Secrets.
Best practices for using Kubernetes External Secrets
To ensure better security and reduce vulnerabilities when using Kubernetes External Secrets, it is recommended to regularly change your secrets. By doing this, you can decrease the risk of any potential threats or unauthorized access.
It is also important to encrypt sensitive information within your secrets. Encryption adds an extra layer of security, making it harder for hackers to understand the data, even if they manage to gain access.
Furthermore, controlling access to your secrets is crucial. Limiting access to only authorized individuals or entities ensures that your secrets are only accessible to those who genuinely need them.
Components of Kubernetes External Secrets
Before implementing Kubernetes External Secrets in your system, it’s important to understand its key components.
Access control ensures that only authorized users have the necessary permissions to access and manage the secrets. You can use Kubernetes RBAC (Role-Based Access Control) to define specific access policies, giving you fine-grained control over who can access the secrets.
Encryption methods are crucial for securing the secrets stored in Kubernetes External Secrets. You can use encryption algorithms like AES (Advanced Encryption Standard) to encrypt the secrets both at rest and in transit. This ensures that even if someone gains unauthorized access to the secrets, they won’t be able to read them without the decryption key.
Secret management involves securely storing, retrieving, and updating secrets. Kubernetes External Secrets seamlessly integrates with external secret stores such as AWS Secrets Manager or HashiCorp Vault. This allows you to centrally manage and securely store your secrets, making it easier to control access and ensure their confidentiality.
Limitations of Kubernetes Secrets and the Need for External Secrets
If you want to improve the security of your system and overcome the limitations of Kubernetes Secrets, you should consider using an external secrets solution. Many expert Kubernetes developers started with trial-and-error.
While Kubernetes Secrets provide a convenient way to store and manage sensitive information, they have some drawbacks that can affect the overall security of your system.
One major drawback is that secrets are stored in plain text within the Kubernetes cluster, which makes them vulnerable to unauthorized access. Furthermore, Kubernetes Secrets do not integrate well with external secret management systems, limiting their ability to securely retrieve and manage secrets from external sources.
By implementing an external secrets solution, you can address these limitations and strengthen the security of your system.
External secrets solutions offer stronger encryption, better access control, and improved integration capabilities, allowing you to securely store and manage secrets in a more robust and flexible manner.
Configuring External Secrets Operator for Kubernetes
To configure the External Secrets Operator in Kubernetes, you can follow the provided documentation for step-by-step instructions. This operator allows you to manage secrets outside of the Kubernetes cluster, which gives you more flexibility and control over sensitive information.
To ensure a successful configuration, there are a few best practices you should consider:
- Create a separate namespace specifically for managing external secrets. This helps keep things organized and makes it easier to manage.
- Use RBAC (Role-Based Access Control) to restrict access to the External Secrets Operator and the secrets it manages. This ensures that only authorized users have access to the sensitive information.
- It’s a good idea to create a dedicated service account with limited privileges for the operator. This helps minimize the risk of unauthorized access to your secrets.
- Grant permissions only to the necessary resources and namespaces. By doing this, you can further reduce the risk of unauthorized access and ensure that only the right people have the necessary permissions.
By following these best practices, you can effectively configure the External Secrets Operator in Kubernetes and ensure the secure and efficient management of your external secrets.
For more detailed instructions and further guidance, please refer to the official documentation.
Conclusion
Kubernetes External Secrets offer many benefits and provide a secure way to manage sensitive data in Kubernetes clusters. They make it easier to handle secrets by integrating with external secret stores and enhance security.
Following best practices like encryption and access controls ensures the effective use of External Secrets. While Kubernetes Secrets have limitations, External Secrets provide a stronger solution.
Configuring the External Secrets Operator for Kubernetes allows for smooth integration and efficient secret management.


![F95Zone Games - The Ultimate Guide for 2021 [F95Z Guide] 5 F95Zone Games](https://knowworldnow.com/wp-content/uploads/2021/07/ArTtW5LrK3b-z-0-y-637f48d86203817a9042a857.webp)